Introduction: Why MFA Setup in Entra Matters
Multi-Factor Authentication (MFA) is the principal sign-in method for Microsoft 365 accounts. Microsoft Authenticator MFA for 365 setup establishes a vital layer of protection by requiring you to verify your identity using more than just a password. Your Microsoft 365 tenancy manages MFA from its Entra portal. not your Microsoft 365 admin dashboard.
This guide helps you understand how Microsoft Authenticator MFA for 365 setup works, including:
- Logging into Microsoft Entra with your 365 credentials to configure Microsoft Authenticator.
- Enabling SMS authentication (if your tenancy is configured to allow this).
- Adding a second device for secondary/fallover access
Read our associated article discusses how to backup your MFA credentials. For support notes about restoring services to Microsoft 365 when your MFA credentials are lost, read this article.
Click open the headers below to learn how to create your MFA credentials. Please read through this entire article before starting the proceudure. Be sure to contact us for general advice if you are in doubt. Support options are available for professional assistance.
What Is Microsoft Entra and Why Use It for MFA?
MFA procedures are consistent with an industry move towards passwordless sign-ins. Consumer-level password protection in Gmail, Yahoo, and other platforms is convenient, but password protection alone is inadequate for meeting GDPR Compliance standards in commerce. Even consumer platforms like Gmail now encourage passwordless sign-in. MFA helps to:
- Ensure your 365 account remains accessible
- Helps build compliant GDPR practices
- Reduce the risk of malicious infiltration and identity theft
Microsoft Entra centralizes your security settings, including MFA, passwordless login, and device authentication. If you are a Microsoft 365 user, you or your organization are already using Entra within your tenancy. So, you are not required to subscribe to Entra as an additional service for Microsoft Authenticator MFA for 365 setup.
Benefits of Using Entra for MFA
- Centralized control over authentication methods
- Enhanced security with multiple verification options
- Flexibility to add or remove devices securely
- Compatibility with SMS, app-based, and hardware token methods
Moving towards passwordless sign-in
The IT industry as a whole recognizes that password protection alone is flawed. So, MFA is increasingly adopted as industry players introduce secure passwordless security. This means that MFA, and similar technologies like 2FA, are here to stay. We can argue that you should adopt MFA to comply with GDPR. Instead, the bigger issue is the risk of catastrophic damage damage to your online identity and data. This way, the fact that MFA is “compliant” is incidental.
This is why MFA is the default sign-in method for Microsoft 365, so you and other users in your 365 tenancy users must configure at least one secure MFA method. This is most conveniently accomplished with Microsoft Authenticator app. SMS authentication is optional and we recommended that you use it as an secondary option for sign-in, especially if your tenancy supports SMS authentication. In situations where we have configured 365 MFA for you, or you retain us to support your Microsoft 365 tenancy, we usually configure support for SMS by default.
Step-by-Step: How to Set Up Microsoft Authenticator in Entra
reparation – what you need
MFA pairs your phone with your 365 account. So, you will need your mobile phone. Also, before you begin, check that your Microsoft 365 tenancy supports SMS authentication for end users and that you have access to your usual laptop or desktop computer. If you are not Global Administrator, you can check with your IT manager.
Allow for some flexibility in this workflow. For instance, it might be worth downloading Microsoft Authenticator App from either Apple App Store (iOS) or Google Play Store (Android) before you start. For instance, it is a good idea to check that your phone is capable of downloading Microsoft Authenticator before you begin. If your mobile phone is outdated or unsupported, Microsoft Authenticator App will not be available to you in your store. If so, consider upgrading your device or using SMS authentication.
Workflow to Set Up MFA with Microsoft Authenticator for 365
- Log into Entra Security Info Portal with your laptop/desktop computer:
- Visit https://mysignins.microsoft.com/security-info
- Sign in using your Microsoft 365 credentials.
- Add Microsoft Authenticator:
- Click + Add sign-in method
- Choose Authenticator App
- Follow the prompts to install the app on your mobile device
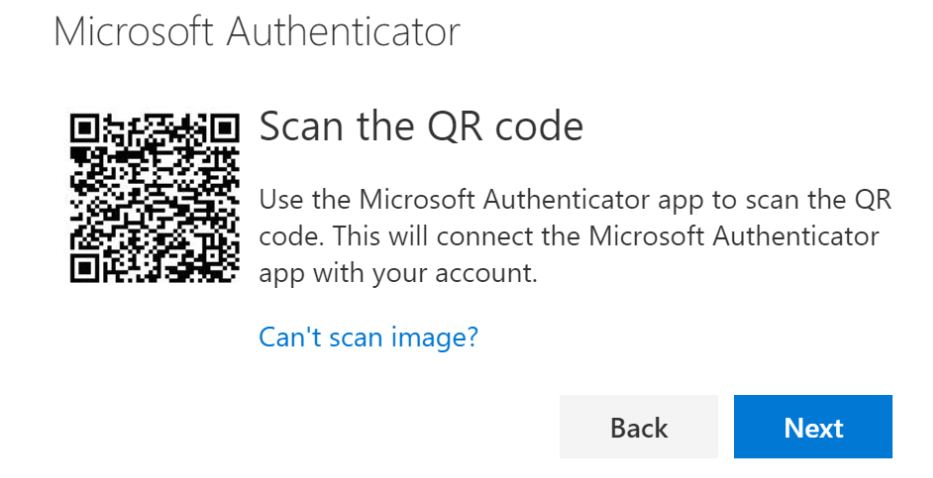
- When you reach a screen showing a QR phone, set your computer aside with the QR code displaying on screen
- Configure your mobile phone:
- On your mobile device, go to the App Store (iOS) or Google Play (Android).
- Search for Microsoft Authenticator and install it.
- With Microsoft Authenticator App open:
- click + (i.e. add account) at top right or left of your screen
- click open the option to scan QR code
- Allow permissions for your app to use your camera
- Scan the QR code showing on your computer screen with your phone
- go back to your computer and click Next
Remember to click
Once you have successfully scanned the QR code with your phone and clicked <Next> on your computer’s security center page (below the QR code), the process is complete. There are two more steps for you to take:
- Test your configuration:
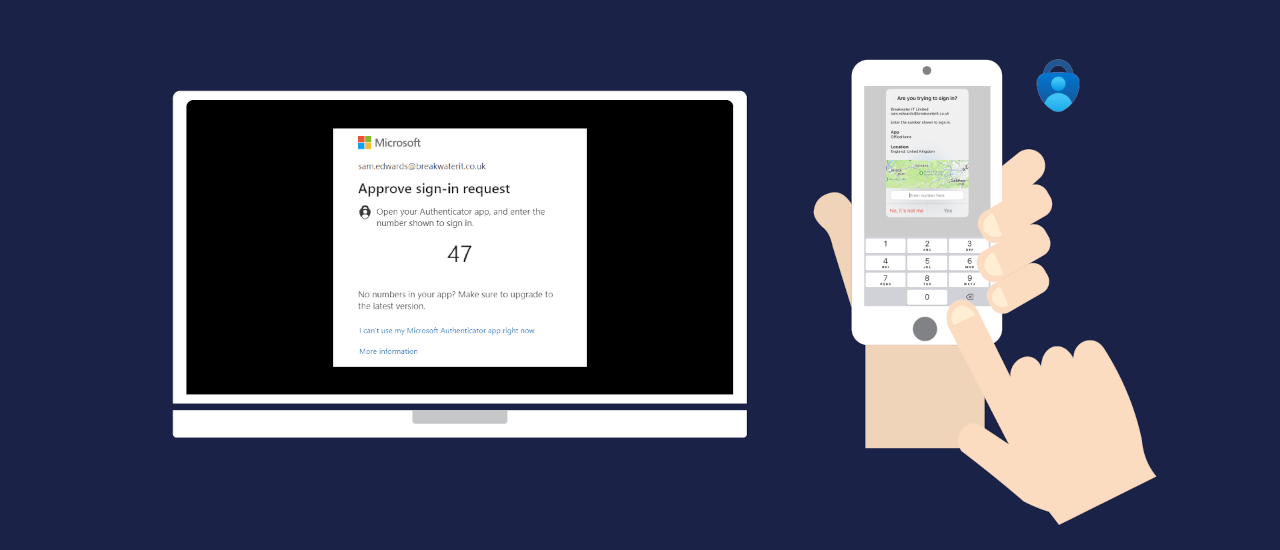
- Entra will send you an MFA input code to test the setup as soon as the server detects the succesful QR scan. The procedure operates in the same way as SMS verification, but using Microaoft Authenticator App. The graphic at the top of this article demontrates what you can expect to see. Having gone to so much trouble to get this far, allow yourself the thrill of seeing this work – it is actually pretty cool!
- Review Microsoft Authenticator App settings, and also your mobile phone settings if necessary to choose personal preferences. For instance:
- You may want verification to include the added security of validating your fingerprint or retina.
- In some instances, your phone might ask you to sing into your phone before you can access Authenticator. Some people prefer this. Others prefer to bypass their phone sign-in screen so that they can respond to their MFA codes faster. This is a matter for personal preference.
- Lastly, you should enable backups and accept periodic updates.
Additional authentication methods using Microsoft Authenticator MFA for 365
The steps above are needed to minimally configure Microsoft Authenticator MFA setup. Read the next section to learn how to add optional authentication using SMS for redundancy.
Also, you can configure Microsoft Authenticator MFA for 365 with a second mobile phone. This is useful where in situations where an email account is shared between two geographically separate offices. Also, setting up Microsoft Authenticator MFA for 365 on an extra phone might be useful in situations where the first phone is at risk of loss or damage.
Create another Global Administrator account
Another way to protect access to your tenancy is to create another Global Administrator. You do not need to have a Microsoft 365 license to add a Global Administrator, and in large organizations the principal Global Administrator does not even use an email account – that way sensitive server-side functions can be handled without the usual risks associated with an email-enabled user. There are some considerations that need addressing to elevate privileges to enable some seucurity functions that are normally reserved for the tenancy owner. We can help configure a secondary Gloabl Administrator.
MFA - What To Do If You Change Your Phone
The easiest way to configure a new mobile phone is to do setup Microsoft Authenticator on your new phone while the old one is still working. With both phones available:
- Log into your security info page with your laptop/desktop
- Click + Add sign-in method
- Choose Authenticator App
- generate a QR code and set the computer aside for the time being
On your NEW phone:
- Install Authenticator and select Work or School account.
- Scan the QR code shown on your computer.
- Approve the authentication request on your new device.
- Remove the old device from the Security Info page.
Enable SMS Authentication (Optional but Recommended)
If your organization allows SMS as an MFA method:
- In the Security Info portal, click + Add sign-in method
- Select “Phone”
- Enter your mobile number and choose Text me a code
- Enter the verification code received via SMS when your mobile phone receives it
SMS is considered less secure than app-based authentication. So, by default, Microsoft Authenticator app will use MFA using either available WiFi or mobile phone signal to authenticate your Microsoft 365 sign-ins. SMS is a valuable backup method—especially if your primary device is unavailable.
Add a Second Device for Secondary Access
Sometimes, it helps to include a second mobile device to authenticate your Microsoft 365 sign-in. This might be necessary where authentication is necessary from two geographically separate locations. In this situation, the same mobile phone cannot be at the each location simultaneously. Also, a second phone might help avoid lockouts. This is optional, and not usually necessary However, if you need to include a second device for authenticating you can configure Microsoft Authenticator MFA for 365 with this additional step:
- Install Microsoft Authenticator on your second mobile phone
- Log into https://mysignins.microsoft.com/security-info from your desktop/laptop computer
- Add a new sign-in method and repeat the QR code scan process
- Be sure to scan the QR code with your SECOND DEVICE per the workflow outlined above
- Verify the second device by approving a test notification
This ensures you can still access your account if your principal mobile phone is lost or damaged.
When SMS is enabled, notice that when trying to sign in with an Autheticator code you will find options in your Authenticator pop up that provide for authentication by other means. This way, if MFA does not authenticate, you can opt to receive a conventional SMS/text.
Summary and Next Steps
Setting up and managing Microsoft Authenticator MFA for 365 helps to secure access to your Microsoft 365 account. If your organization has documentation for compliance, you should update it with your procedures so that you have a stated policy giverning sign-ins.
Next step – backup your MFA credentials
For added security, you can backup your Microsoft Authenticator App sign-in accounts. Even if your mobile phone is configured to backup your data, MFA credentials are excluded from Android/iOS backups unless provisioned in Microsoft Authenticator App.
Read this article to learn how to back up your Microsoft Authenticator settings and avoid losing access. Remember, MFA is now a user-level utility and admins/global admins cannot intervene on a user’s behalf. So, it is important to be sure that organizational users have MFA credential backups to ensure rapid restoration of services if they lose or damage their mobile phones.
Also, consider a stress test to learn what you need to be able to demonstrate to Microsoft if your Global Administrator loses MFA credentials. Read this article to learn about force majeur MFA recovery.
About ComStat.uk: Internet Service Provider Comstat provides IT support, web hosting, and media services including website design, Microsoft 365 setup, and audio/video production, serving businesses across Denbighshire, North Wales and Wirral from Ruthin, and Lancashire and the Northwest from Bolton.